What Is a DDoS Attack and How It Works?
DDoS attacks pose an existential threat to your digital availability. To defend your infrastructure, you must understand what is DDoS protection—the essential shield that filters malicious traffic at the edge. Join Axclusive in the article below as we explore the best practices and platform strategies to secure your network against modern cyber threats.
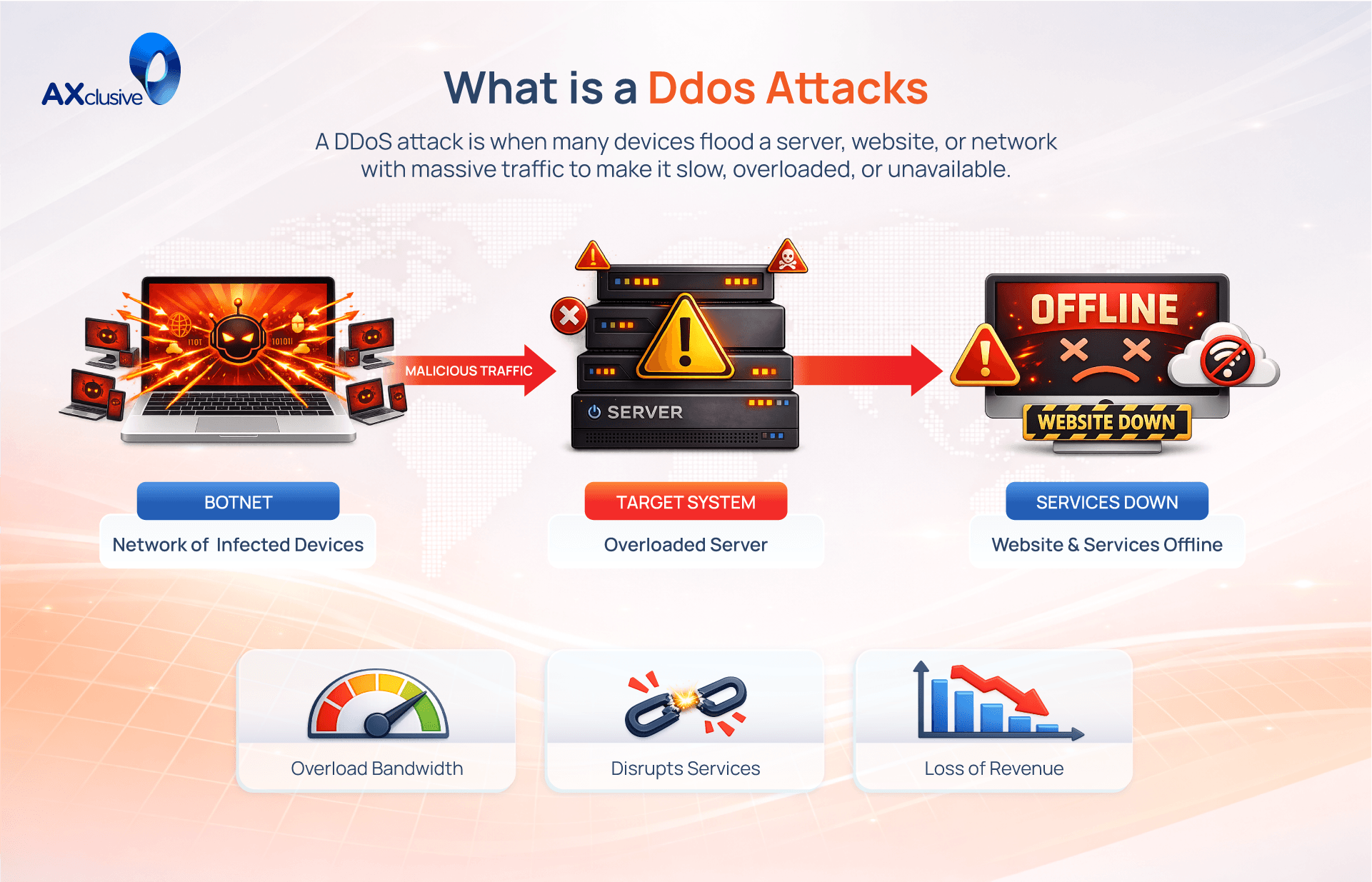
What is a DDoS attack?
A Distributed Denial of Service (DDoS) attack is a malicious attempt to disrupt the normal operations of a targeted server, service, or network by overwhelming it with a massive flood of illegitimate internet traffic. Unlike a standard denial of service incident, these attacks achieve effectiveness by utilizing multiple compromised computer systems, such as infected PCs and vulnerable IoT devices, to act as sources of attack traffic. From a high level, a DDoS attack functions like an unexpected traffic jam clogging a major highway, effectively preventing legitimate users from reaching their destination.
The Purpose Behind a DDoS Attack
The primary objective of a Distributed Denial of Service (DDoS) attack is to cripple a target's ability to serve legitimate traffic. By flooding servers with overwhelming request volumes, attackers force services to slow down or crash entirely. This disruption prevents users from accessing websites, purchasing products, or engaging with digital platforms. For businesses, this translates into immediate downtime, where employees lose access to critical email systems, internal applications, and essential business tools.
Attackers launch these campaigns for various strategic and malicious reasons:
Hacktivism: Ideologically driven groups target organizations that conflict with their personal, political, or social viewpoints to make a public statement.
Extortion: Cybercriminals threaten to disable a company's web infrastructure unless a ransom is paid, directly impacting corporate revenue and operations.
Business Competition: Dishonest entities may deploy these attacks to knock a competitor offline, effectively capturing market share or damaging their rival's professional reputation.
Cyber Warfare: Nation-states utilize large-scale DDoS attacks to destabilize critical infrastructure, cripple government services, or create strategic advantages during geopolitical conflicts.
Malicious Entertainment: Some attackers seek personal thrill, using these disruptive events to experiment with cybercrime or simply to cause chaos within popular digital ecosystems.
How a DDoS Attack Works
A DDoS attack functions by leveraging a distributed network of internet connected machines, commonly known as a botnet. To build this infrastructure, attackers infect thousands of individual devices ranging from standard computers to vulnerable IoT hardware with malicious software. Once infected, these devices become bots or zombies, allowing the attacker to control them remotely.
By sending a centralized command to this entire network, the attacker forces every bot to simultaneously flood the target IP address with a massive volume of connection requests. This concentrated, high frequency traffic eventually exhausts the target server resources or network bandwidth, causing it to crash or become unresponsive to legitimate user requests. Because each bot is a genuine device with a real IP address, distinguishing between this malicious flood and normal user traffic remains the greatest challenge for network security teams.
Common Types of DDoS Attack
DDoS attacks are categorized by the specific layer of the network they target. By understanding these attack vectors, security teams can better identify and filter malicious traffic before it compromises system availability. Attacks generally fall into three distinct classifications: Application Layer, Protocol, and Volumetric.
Application Layer Attacks
Often called Layer 7 attacks, these target the top of the OSI model where web pages are generated. Attackers send seemingly legitimate requests that force the server to perform resource-intensive tasks, such as loading multiple files or running complex database queries. Because these requests mimic real user behavior, they are exceptionally difficult to filter. A common example is the HTTP Flood, which behaves like thousands of users repeatedly hitting the "refresh" button on a website, quickly exhausting server memory and CPU.
Protocol Attacks
Protocol attacks, also known as state-exhaustion attacks, target vulnerabilities in Layers 3 and 4 of the network stack. They focus on consuming the limited state tables of network equipment like firewalls, load balancers, and routers. A classic example is the SYN Flood. The attacker exploits the TCP handshake process by sending a flood of connection requests but never finalizing the connection. This leaves the server waiting for responses that never arrive, eventually locking up its resources and preventing it from accepting any legitimate connections.
Volumetric Attacks
Volumetric attacks are the most common form of DDoS, designed to saturate the available bandwidth between a target and the wider internet. By generating massive amounts of data traffic, attackers effectively block all inbound and outbound access. A frequent method is DNS Amplification. In this scenario, the attacker sends a small request to an open DNS server while spoofing the victim's IP address. The server then sends a much larger response to the victim. By using many such servers, the attacker amplifies the traffic volume, easily overwhelming the target’s network pipe with a flood of data.
DDoS Attack Mitigation Methods
Mitigating a Distributed Denial of Service (DDoS) attack requires the ability to distinguish between legitimate user traffic and malicious request floods. Because modern attacks often use multi vector tactics targeting multiple layers of the protocol stack simultaneously, a single defense strategy is rarely enough. Effective protection requires a layered approach that filters bad requests without disrupting genuine customer access. The following methods are the standard industry techniques for neutralizing these threats.
Blackhole Traffic Routing
Blackhole filtering is the most extreme mitigation technique. When an attack is identified, the network administrator directs all incoming traffic (both malicious and legitimate) into a null route or blackhole, where it is dropped from the network. While this prevents the target server from crashing, it is counterproductive because it effectively completes the attacker's goal: making the service inaccessible. This method is usually reserved as a last resort measure to protect the broader network infrastructure when an attack becomes unmanageable.
Traffic Rate Control
Rate limiting restricts the number of requests a server or API will accept from a specific source within a set timeframe. This is highly effective at slowing down automated bots, web scrapers, and brute force login attempts. While rate control is an essential component of a broader security strategy, it is rarely sufficient on its own to stop a massive, coordinated DDoS flood. It works best when combined with other filtering rules to create a defense in depth posture.
Web Application Firewall Protection
A Web Application Firewall (WAF) acts as a reverse proxy, sitting directly between the public internet and your origin server. It inspects Layer 7 (application layer) traffic to identify and block malicious patterns. By applying a custom set of rules, the WAF can recognize common DDoS tools and filter out illegitimate HTTP requests before they reach your server. The primary advantage of a WAF is the ability to implement rapid, custom rules in response to emerging, adaptive threats in real time.
Anycast Traffic Distribution
Anycast network diffusion is a highly effective way to absorb large scale volumetric attacks. By using an Anycast network, inbound traffic is scattered across a globally distributed cluster of servers. This is analogous to channeling a massive, rushing river into many smaller, manageable streams. Because the attack traffic is diffused across dozens or hundreds of data centers worldwide, no single server node is overwhelmed. This allows the network to absorb the flood and render it harmless, ensuring legitimate users still have a clear path to the service.
Frequently Asked Questions
Is a DDoS attack illegal?
Yes, launching a DDoS attack is a serious crime under cybercrime laws in most countries, including the Computer Misuse Act in Singapore and the Computer Fraud and Abuse Act in the United States. Perpetrators face severe penalties, including heavy fines and imprisonment, as these attacks intentionally disrupt critical infrastructure and cause significant financial damage.
Can you stop a DDoS attack?
Yes, but effective mitigation requires proactive preparation. You cannot stop an attack from being launched, but you can neutralize it before it impacts your services by using advanced mitigation platforms. Solutions like Anycast network diffusion, Web Application Firewalls (WAF), and automated traffic filtering can absorb malicious floods, ensuring your resources remain accessible to legitimate users.
How long will a DDoS attack last?
The duration of a DDoS attack is highly unpredictable. Some attacks are brief "bursts" intended to test your defenses, lasting only a few minutes, while others can persist for days or even weeks. Sophisticated, adaptive attacks often cycle through different vectors to wear down security teams, making it essential to have always-on mitigation solutions rather than relying on manual intervention.
Effective DDoS protection is essential for maintaining digital resilience. By establishing traffic baselines, prioritizing critical assets, and deploying an automated mitigation platform, you can successfully neutralize modern cyber threats. Axclusive trusts this guide helps you fortify your infrastructure, ensuring continuous uptime and security for your business.
Discover what is a DDoS attack and learn how to safeguard your network from disruptive threats. Contact us today to build a stronger, smarter defense against modern cyber attacks