What Is TCP? How It Works in Networking
How does data arrive perfectly intact across the unpredictable internet? The answer lies in understanding what is tcp. As the foundational rulebook for digital communication, the Transmission Control Protocol guarantees that information reaches its destination without errors or missing pieces. Join Axclusive in the article below as we explore how this essential protocol powers modern networking.
What is TCP ?
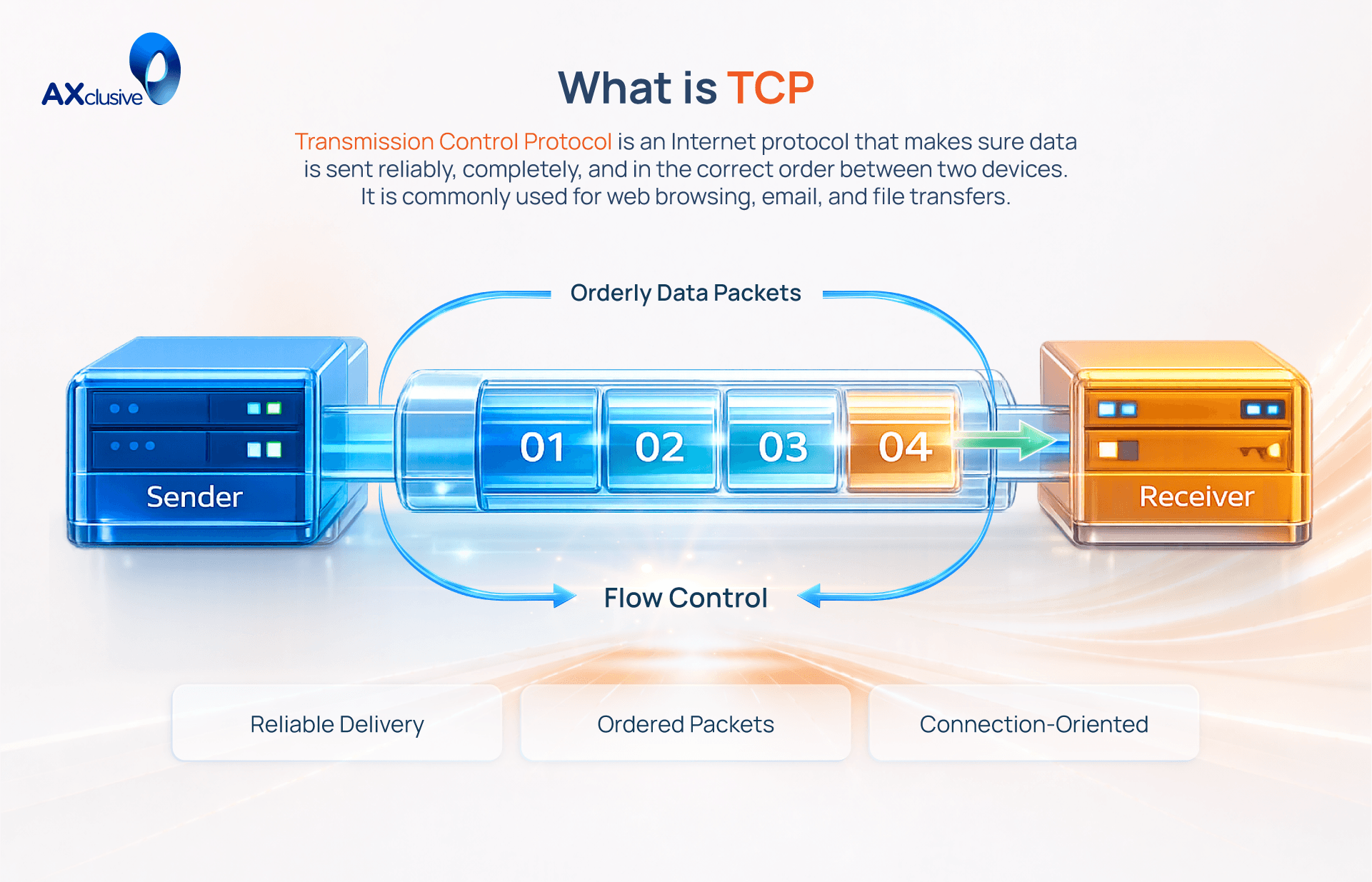
Transmission Control Protocol provides a reliable way to exchange data across computer networks. It acts as the primary standard for the internet protocol suite. This technology operates at the Transport Layer of the OSI model. TCP ensures that all information reaches its destination without errors or missing segments. It uses a connection-oriented method to link two devices before any data flows. The protocol assigns a unique sequence number to every data packet. This numbering allows the receiving computer to rebuild the original file in the correct order. TCP requires an acknowledgment from the receiver for every packet delivered. If a packet goes missing or suffers damage, the system sends it again automatically. It also monitors network traffic to prevent congestion. This prevents a sender from overwhelming a receiver with too much data at once.
How TCP Works in Data Communication
The Transmission Control Protocol follows a strict, step by step process to guarantee accurate data delivery. It manages the entire lifecycle of a network conversation from start to finish. This operation occurs through four distinct phases.
Establishing the Connection: TCP requires a formal connection before moving any data. It establishes this link using a three way handshake. The sending device transmits a SYN (synchronize) message to request access. The receiving server answers with a SYN ACK (synchronize and acknowledge) message. Finally, the sender replies with an ACK message. This confirms the open connection and prepares both devices for data transfer.
Segmenting the Data: The protocol cannot send large files all at once. It breaks the data down into smaller, manageable pieces called segments. The system assigns a unique sequence number to every segment. This numbering system acts as an assembly guide. It allows the receiving device to rebuild the message in the exact original order.
Transmitting Data and Resolving Errors: Data travels across the open connection in both directions. The receiver calculates a mathematical value called a checksum on every incoming segment to detect errors. If the checksum fails, the receiver drops the corrupted segment and requests an immediate retransmission. The receiver also sends an acknowledgment message for every successful segment. During this phase, the protocol adjusts the transmission speed continuously to prevent network congestion and hardware overload.
Closing the Connection: The protocol closes the session through a formal four step termination process once the data transfer ends. The sender transmits a FIN (finish) message. The receiver acknowledges this message. The receiver then sends its own FIN message to indicate it has finished its part of the communication. The sender acknowledges the final message. This structured closing sequence guarantees no data gets lost or abandoned at the end of the transfer.
Different Types of TCP Implementations
TCP is a singular protocol, but engineers have developed various versions based on how they handle network congestion. As internet speeds and latency challenges have evolved, these congestion control algorithms have become more sophisticated. They dictate how aggressively TCP sends data and how quickly it recovers from lost packets.
TCP Reno: A foundational algorithm used widely in early networking. It introduced "Fast Recovery," allowing a connection to recover from a single dropped packet quickly without drastically reducing the overall transmission speed.
TCP New Reno: An evolution of the Reno algorithm. It is specifically designed to handle situations where multiple packets are lost within the same transmission window, ensuring a smoother and more efficient recovery process.
TCP Vegas: Unlike earlier versions that react after a packet is lost, Vegas attempts to predict and prevent congestion. It monitors slight changes in Round Trip Time (RTT) to slow down data transmission before network queues overflow. While highly efficient, its complexity has limited its widespread adoption.
TCP CUBIC: The current default congestion control algorithm for Linux operating systems. It is highly optimized for modern, high-speed, and long-distance networks, ensuring maximum bandwidth utilization over vast geographical areas.
TCP BBR: Developed by Google, BBR (Bottleneck Bandwidth and Round-trip propagation time) represents a modern approach. It measures the actual bottleneck bandwidth and RTT to optimize data delivery on contemporary, complex internet paths, often significantly outperforming older loss-based algorithms.
Core Features of TCP Protocol
The Transmission Control Protocol relies on a strict set of rules to ensure data integrity across complex networks. These features distinguish it from faster, connectionless protocols by prioritizing accuracy and order over raw speed. Network engineers rely on these core functions to build stable applications.
Connection-Oriented Setup: TCP mandates a formal connection between the sender and receiver before any data transfers. This established link remains actively open and monitored until the complete file is delivered and the session is formally terminated.
Sequence Numbering: To guarantee ordered delivery, TCP assigns a unique sequence number to every byte of data it transmits. The receiving device uses these numbers to reassemble the fragmented data segments into the correct original order, eliminating scrambled files.
Automatic Retransmission: The protocol requires the receiver to send an acknowledgment (ACK) for every delivered segment. If the sender does not receive this ACK within a specific timeframe, it automatically retransmits the missing packet, ensuring reliability even over unstable Wi-Fi connections.
Full-Duplex Communication: TCP supports simultaneous two-way traffic. Data can flow from the sender to the receiver and from the receiver back to the sender at the exact same time, making it ideal for interactive applications.
Checksum Error Detection: Every data segment includes a mathematical checksum in its header. The receiving device recalculates this checksum upon arrival; if the numbers do not match, the segment is deemed corrupted and immediately discarded, triggering a retransmission request.
Flow Control (Windowing): TCP prevents a fast sender from overwhelming a slow receiver. It uses a "sliding window" mechanism where the receiving device constantly signals how much data it can currently process, allowing the sender to adjust its transmission rate accordingly.
Dynamic Congestion Control: Beyond managing the receiver's capacity, TCP monitors the overall health of the network. If it detects dropped packets or severe delays indicating network congestion, the protocol automatically throttles back its sending speed to alleviate pressure on the infrastructure.
Common Applications of TCP Protocol
The Transmission Control Protocol is the foundation for almost every critical internet service. Because it guarantees data integrity and ordered delivery, developers rely on TCP for any application where a missing packet would cause the system to fail. The following digital services depend entirely on this protocol to function correctly.
Web access via HTTP and HTTPS
Every time you load a webpage, your browser relies on TCP. Websites transmit text, images, and code in thousands of small packets. TCP ensures these packets arrive completely and assembles them in the exact order the developer intended. Without this protocol, web pages would load with broken images or missing text. Even when a site uses HTTPS for encryption, TCP still manages the underlying reliable delivery of the encrypted data.
Email communication protocols
Email systems cannot tolerate data loss. Whether you use SMTP to send a message or IMAP and POP3 to retrieve it, the entire contents must arrive intact. TCP ensures that every character of your text and every byte of an attached document transfers successfully. If a packet containing part of a PDF attachment drops due to network congestion, TCP automatically requests a retransmission, guaranteeing the file is not corrupted upon arrival.
Secure and standard file transfers
Moving large files across a network via FTP (File Transfer Protocol) or SFTP (Secure File Transfer Protocol) requires absolute accuracy. TCP handles these massive data loads by dividing the files into numbered segments. It monitors the transit, reorders the segments at the destination, and replaces any lost pieces. This mechanism ensures that the downloaded file is a perfect, identical copy of the original uploaded file.
Remote system access and control
IT administrators use tools like SSH (Secure Shell) or legacy Telnet to manage servers remotely. In these environments, every single keystroke matters. A dropped packet could turn a harmless command into a destructive one. TCP maintains a stable, continuous connection between the user and the remote machine, ensuring that commands are transmitted reliably and executed in the exact sequence they were typed.
Benefits of Using TCP in Networking
TCP remains the foundational protocol for the internet because it prioritizes accuracy over raw speed. Network engineers choose this connection-oriented approach when data integrity is non-negotiable. Its design provides several critical advantages that ensure digital communication remains stable across unpredictable global networks.
Error-Free Data Transfer: TCP acts as a quality control mechanism. It constantly monitors for corrupted or missing packets and automatically retransmits them, guaranteeing the final delivery is completely accurate.
Ordered Delivery: The protocol assigns a sequence number to every piece of data. This ensures the receiving device rebuilds the file in the exact order it was sent, preventing scrambled or unusable information.
Flow Control: TCP prevents a fast server from overwhelming a slower client device. By communicating its processing capacity, the receiver dictates the transmission speed, eliminating data loss at the endpoint.
Congestion Control: The protocol actively monitors the health of the entire network path. If it detects traffic jams or dropped packets, it slows down the sending speed to reduce overall network congestion.
Reliable Communication: Because it guarantees delivery and manages errors, TCP is the only viable choice for critical applications like banking, email, and secure file transfers.
Universal Standardization: As a core component of the internet protocol suite, TCP is globally supported. Every major operating system, router, and firewall natively understands and processes TCP traffic seamlessly.
Guarantee your critical data arrives intact with the technical insights provided in this guide. Axclusive equips you with the knowledge to navigate complex network transmissions. Apply these principles to build a resilient and error-free infrastructure for your business today.
Learn what is TCP and how it ensures reliable data transmission. Contact us to optimize your network performance and connectivity.