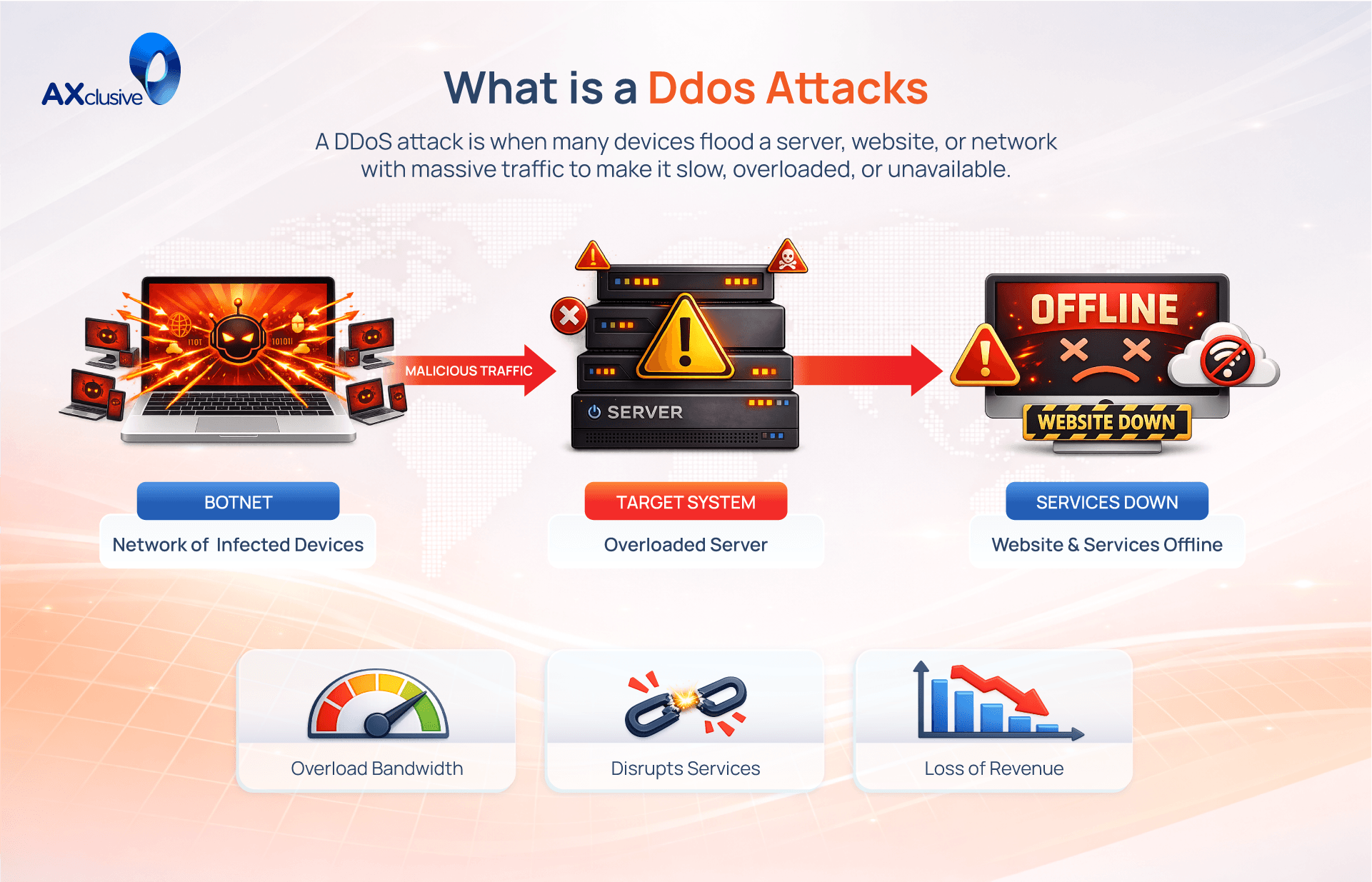
How to Prevent DDoS Attack and Protect Your Network?
DDoS attacks can paralyze your digital infrastructure in seconds. To maintain uptime, you must transition from reactive patching to a proactive defense strategy. Join Axclusive as we explore essential best practices to fortify your network and ensure your services remain available against modern cyber threats.
How to Prevent DDoS Attacks with Best Practices
Defending against Distributed Denial-of-Service (DDoS) attacks requires a proactive, multi-layered security strategy. Because attackers constantly evolve their tactics to mimic legitimate traffic, reactive measures are often insufficient. By implementing the following best practices, you can fortify your network architecture and ensure business continuity even when targeted.
Understand Your Normal Traffic Patterns
You cannot detect an anomaly if you do not know what "normal" looks like. Establish a baseline for your network traffic by monitoring typical volume, packet types, and peak usage hours. This baseline acts as your reference point; when traffic spikes or deviates from this standard, your security tools can instantly flag the activity as a potential DDoS threat rather than a surge in popularity.
Build a Denial of Service Response Plan
Do not wait for an attack to decide how to respond. Create a formal response plan that defines exactly who is responsible for what during a crisis. Your plan must include a clear system checklist, an escalation procedure, and a list of key internal and external contacts. Ensure your team is trained to execute this plan quickly to minimize downtime and prevent panic.
Strengthen Network Resilience
Your infrastructure must be built to withstand pressure. Avoid single points of failure by distributing your servers and data centers across different physical locations and network segments. Use redundant DNS servers and implement traffic-filtering tools that can withstand stress. A resilient network architecture ensures that even if one component is overwhelmed, other segments can maintain service availability.
Maintain Strong Cyber Hygiene
Basic security practices are your first line of defense. Hackers often gain access to your network through weak points before launching a larger attack. Enforce strong password policies, mandate multi-factor authentication (MFA), and ensure all security patches are applied immediately. A well-secured network prevents attackers from establishing a foothold and using your own internal systems to amplify their attacks.
Increase Available Bandwidth
While extra bandwidth will not stop a massive volumetric attack, it provides a crucial buffer. By over-provisioning your network capacity, you gain time to identify and mitigate an attack before your resources are completely exhausted. Think of this as widening the highway; it prevents minor traffic spikes from becoming total gridlock and keeps services responsive while mitigation tools activate.
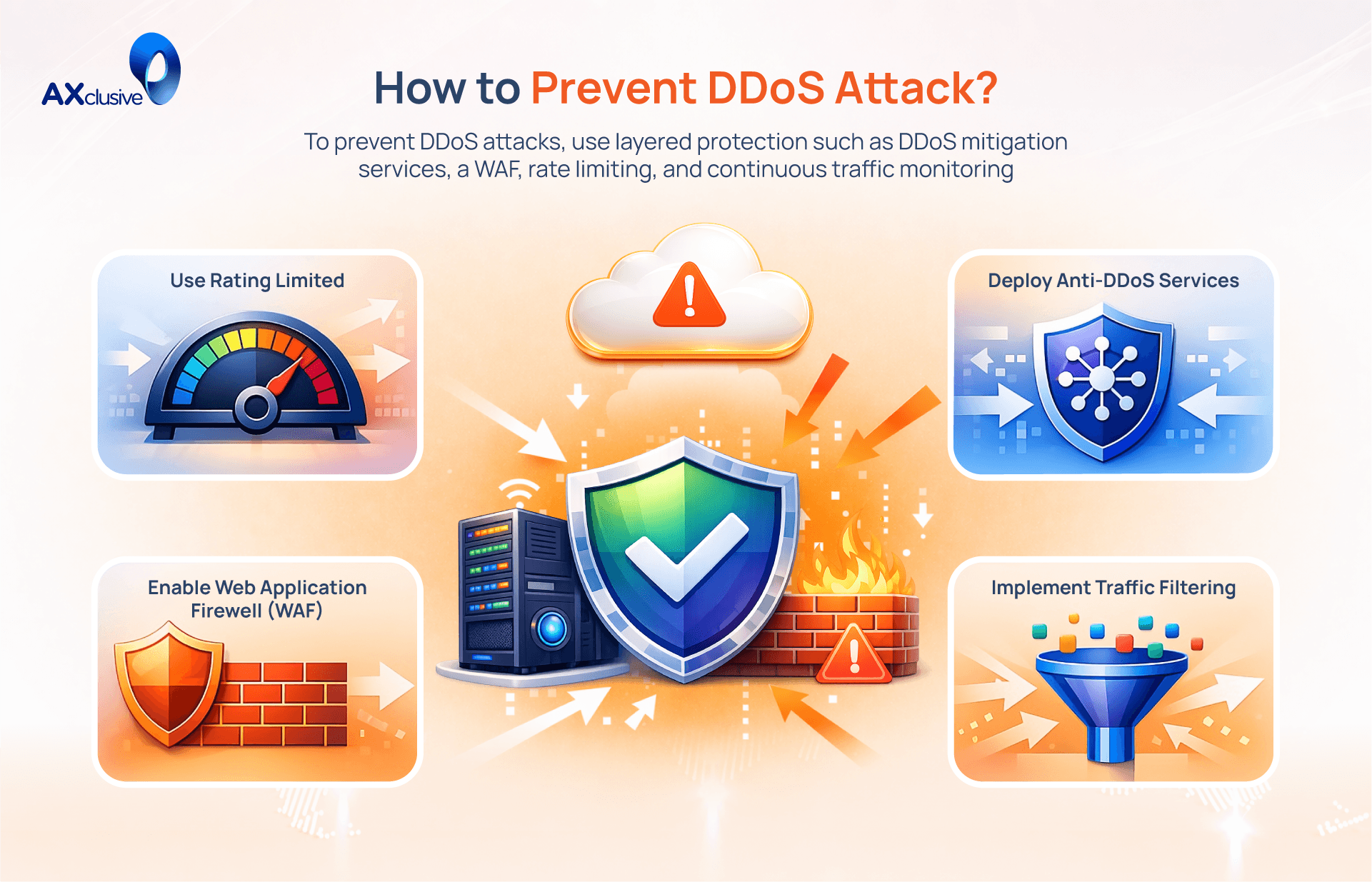
Deploy Dedicated Mitigation Tools
Standard firewalls often fail against sophisticated, high-volume DDoS floods. Deploy dedicated mitigation solutions, such as Web Application Firewalls (WAFs) and specialized traffic-scrubbing appliances. These tools are purpose-built to filter malicious requests at the edge, removing threats before they ever reach your primary server or internal network.
Shift Protection to the Cloud
Moving your defense to the cloud is one of the most effective ways to stop large-scale attacks. Cloud-based protection services offer nearly infinite bandwidth to absorb traffic floods that would crash an on-premises data center. They provide an "always-on" shield that filters traffic in the cloud, ensuring only clean, legitimate requests reach your local infrastructure.
Recognize the Early Signs of an Attack
Attackers often perform "probing" traffic before launching a full-scale flood. Train your team to recognize the symptoms: inexplicably slow performance, sudden outages, or high demand from a single IP address. A sudden surge in traffic—especially from a narrow set of sources—is often the earliest indicator that a coordinated flood is underway.
Use Managed DDoS Protection Services
If your team lacks the resources to manage constant threats, outsource to a "DDoS-as-a-Service" provider. These managed services specialize in scaling resources and responding to attacks around the clock. They provide the expertise and infrastructure needed to recover from complex events far more efficiently than an in-house team could alone.
Monitor Continuously for Unusual Activity
Real-time analysis is non-negotiable. Continuous monitoring allows you to detect the subtle oddities that precede a larger campaign. Use threat intelligence platforms and flow analysis to spot malicious requests in real time. By automating this oversight, your organization can move from reactive firefighting to proactive, automated mitigation.
Frequently Asked Questions
Can DDoS attacks be prevented?
While you cannot prevent an attacker from attempting a DDoS attack, you can effectively neutralize one before it impacts your services. By maintaining robust network resilience, implementing proactive traffic monitoring, and deploying cloud-based mitigation tools, organizations can absorb and filter malicious traffic, ensuring legitimate users remain unaffected.
What is the solution for a DDoS attack?
The primary solution is to utilize an "always-on" DDoS mitigation service, such as a cloud-based scrubbing platform. These services automatically detect anomalous traffic spikes and reroute incoming requests through a high-capacity filter that discards malicious packets while allowing genuine user traffic to pass through to your origin server.
Can Attackers Combine Multiple DDoS Methods?
Yes. Sophisticated attackers frequently use "multi-vector" attacks. They might combine a volumetric flood (targeting network bandwidth) with an application-layer attack (targeting server resources like HTTP requests). This strategy is designed to overwhelm security teams by attacking multiple layers of the protocol stack simultaneously.
Can a Firewall Block a DDoS Attack?
A traditional firewall is often insufficient against large-scale DDoS attacks. While firewalls can block basic, unauthorized access, they are not designed to handle the massive traffic volume of a volumetric DDoS flood. The firewall itself often becomes the bottleneck, crashing under the sheer request count. Effective defense requires dedicated DDoS mitigation tools, such as Web Application Firewalls (WAF) or cloud-based edge filtering.
Proactive defense is the cornerstone of a resilient digital infrastructure. By establishing traffic baselines, prioritizing critical assets, and deploying automated mitigation services, you can successfully neutralize even the most sophisticated cyber threats. Axclusive trusts this guide has provided the foundational knowledge you need to learn how to prevent DDoS attacks and ensure continuous uptime for your business.
Discover how to prevent DDoS attack and keep your network resilient against evolving cyber threats. Contact us now to strengthen your protection and stay ahead of attacks