What Are Packets in Networking? Structure, Transmission, and Security
Every email you send and every video you stream is made possible by a fundamental unit of data. So, what is a packet? It is the small, addressed ‘parcel’ of information that forms the building block of all modern networks. Join Axclusive ISP in the article below as we explore the structure and journey of these essential data packets.
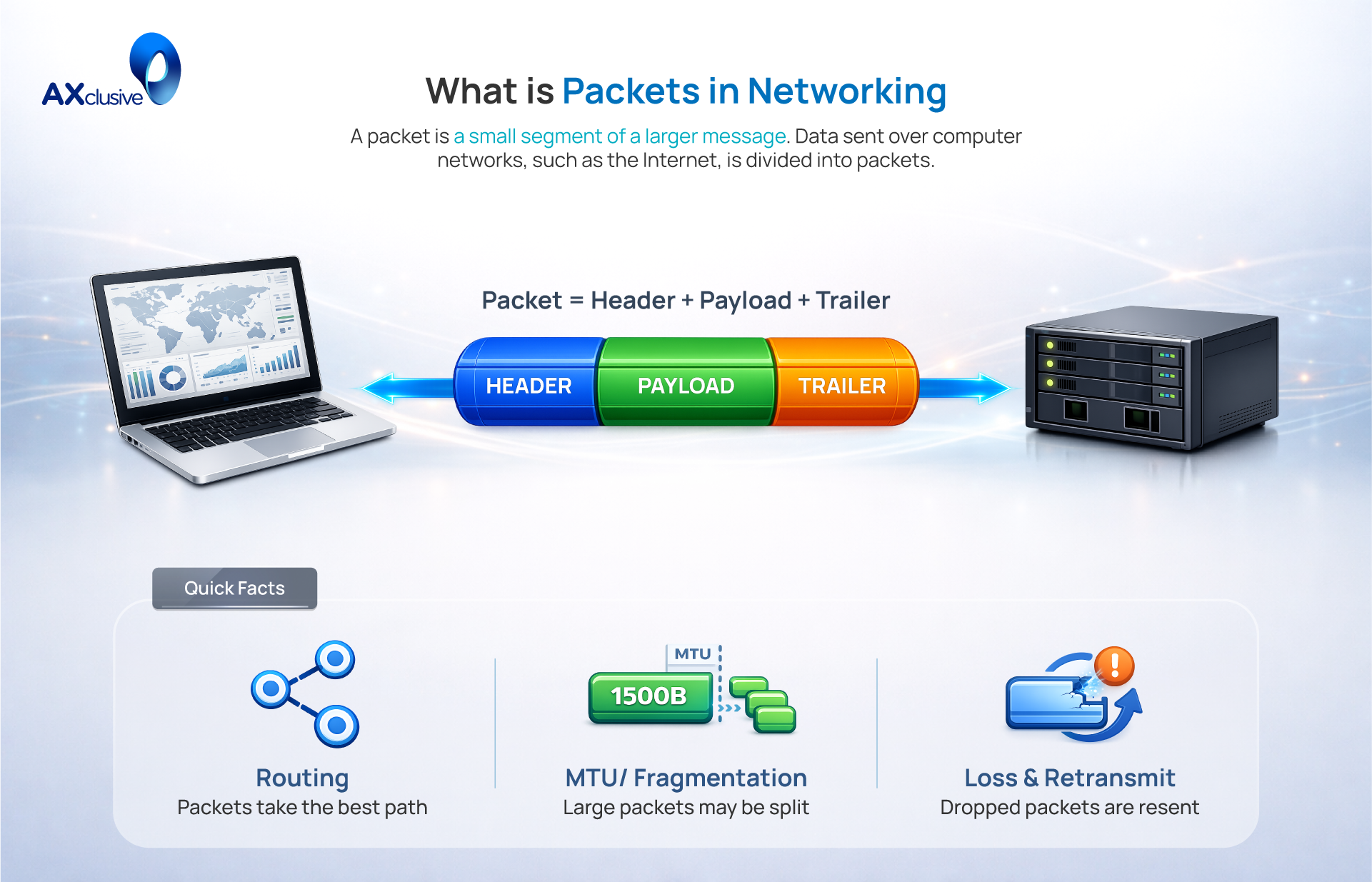
What is Packet In Networking?
In computer networking, a packet is the fundamental unit of data for all modern communication. Instead of sending a large file as one continuous stream, data is broken down into smaller, more manageable segments. Each packet consists of two primary components: the payload, which contains the actual user data, and the header. The header acts as a routing label, containing critical control information such as the source and destination IP addresses, the protocol in use, and a sequence number. Upon arrival, the receiving device uses this information to reassemble the packets in the correct order, reconstructing the original message.
Packet Types in Network Communication
In network communication, packets are classified by their function. While all packets share a basic structure, their purpose dictates the information they carry and how the network treats them. Understanding these types is essential for managing and securing network traffic.
- Data Packets: These are the most common packets and serve the primary purpose of the network: to transport user information. The content of a webpage, the text of an email, or a segment of a video stream is carried within the payload of data packets. They are the cargo of the internet.
- Control Packets: These packets do not carry user data. Instead, they manage the communication session itself. They are used to establish connections, acknowledge the receipt of data, manage traffic flow, and terminate sessions. The classic TCP three-way handshake (SYN, SYN-ACK, ACK) is performed entirely with control packets.
- Routing Packets: A specialized type of control packet, these are used exclusively by routers to communicate with each other. They contain updates about network topology and path availability, allowing routers to build and maintain accurate routing tables. Protocols like BGP and OSPF rely on these packets to keep the internet running efficiently.
- Diagnostic and Service Packets: This category includes packets used for network troubleshooting and essential services. ICMP packets, used by tools like ping and traceroute, report errors and test connectivity. DNS packets are used to query servers to resolve domain names into IP addresses.
How a Packet Is Transmitted
The transmission of a network packet is a systematic process that ensures data moves reliably from a source to its destination. This journey involves several distinct stages governed by network protocols.
First, the sending device segments the larger message into smaller data chunks. Each chunk becomes the payload of a new packet. This payload is then encapsulated with headers. The Transport Layer adds a header with port numbers and sequence numbers (for reassembly), while the Network Layer adds another header containing the source and destination IP addresses.
Next, the packet is sent to the local network, where routers take over. At each router, the device examines the destination IP address in the packet’s header. It consults its internal routing table to determine the most efficient next hop on the path. The packet is then forwarded to that next device. This hop-by-hop decision process repeats across the internet.
Finally, upon arrival at the destination, the packets are processed. The receiving device uses the sequence numbers in the headers to reassemble the payloads in the correct order, reconstructing the original message. It also performs an integrity check using a checksum value in the header. If a packet is missing or corrupted, protocols like TCP will automatically request a retransmission of only that specific packet, ensuring the data is complete and accurate.
Why Packet-Based Communication Matters
Packet-based communication, or packet switching, is the foundational architecture of the internet because it provides a superior model for efficiency, resilience, and scale. This approach is not just a technical detail; it is the reason the internet can function as a global, reliable system.
- Network Efficiency: Packet switching allows network infrastructure to be shared dynamically. Unlike older methods that required a dedicated circuit for a single conversation, packets from many users can traverse the same lines, dramatically increasing the network’s overall capacity and lowering operational costs.
- Enhanced Reliability: The model enhances data integrity. By breaking a large file into small packets, any transmission error is isolated to a single, small unit. This allows protocols to request a retransmission of only the missing or corrupted packet, rather than the entire file, making communication far more reliable.
- Inherent Resilience: It creates a fault-tolerant network. Since each packet is independently addressed, it can be routed dynamically around network congestion or hardware failures. This decentralized approach ensures there is no single point of failure, allowing the network to “self-heal” and maintain connectivity.
- Universal Interoperability: A standardized packet format allows different types of networks (e.g., fiber, Wi-Fi, cellular) to communicate seamlessly. This universal standard is the key that has allowed the internet to scale from a small project to a global system connecting billions of diverse devices.
Network Protocols Built on Packets
Packets are the fundamental data units, but protocols define the rules for how they are managed and transmitted. These protocols work together in a layered stack to ensure data gets from source to destination, with different protocols handling addressing, reliability, and speed.
Internet Protocol (IP)
The Internet Protocol (IP) is the principal network layer protocol responsible for logical addressing and routing. Its sole job is to attach a header to a packet that contains the source and destination IP address, much like putting an address on an envelope. Routers across the internet use this IP address to forward the packet toward its final destination. IP operates on a “best-effort” delivery model, meaning it does not guarantee that packets will arrive, be free of errors, or arrive in order. It simply provides the addressing system for two main versions: IPv4 (32-bit addresses) and the newer IPv6 (128-bit addresses).
Transmission Control Protocol (TCP)
While IP handles addressing, the Transmission Control Protocol (TCP) ensures that data arrives reliably and in the correct order. TCP is a connection-oriented protocol, meaning it establishes a formal connection (via a “three-way handshake”) before any data is sent. It accomplishes reliability through a system of sequence numbers and acknowledgments (ACKs). The receiver confirms which packets it has received, and the sender retransmits any packets that were not acknowledged. Because of its high reliability, TCP is the standard for applications where data integrity is critical, such as web browsing (HTTP/HTTPS), email (SMTP), and file transfers (FTP).
User Datagram Protocol (UDP)
The User Datagram Protocol (UDP) is the lightweight, “fire-and-forget” alternative to TCP. UDP is a connectionless protocol, meaning it sends data packets (called datagrams) without establishing a prior connection or checking for receipt. It prioritizes speed and low overhead by sacrificing the reliability guarantees of TCP; it does not reorder packets or retransmit lost ones. This makes it ideal for real-time applications where a slight data loss is preferable to the delay caused by retransmissions, such as online gaming, Voice over IP (VoIP), and live video streaming.
Packet-Based Security Threats
Because packets are the fundamental units of all network communication, they are also a primary target for malicious activity. Attackers can intercept, forge, or manipulate packets to compromise data, disrupt services, and gain unauthorized access. Understanding these vulnerabilities is the first step toward building a secure network.
Network Sniffing
Network sniffing, also known as eavesdropping, is the act of capturing and inspecting packets as they travel across a network. On unencrypted networks, such as public Wi-Fi, attackers can use sniffing tools to read sensitive information—including passwords and personal data—directly from the packet payload. The primary defense against this threat is strong, end-to-end encryption. Protocols like HTTPS and TLS, along with the use of a reputable VPN, render sniffed data unreadable to an attacker.
Malicious Packet Injection
This attack involves an adversary inserting unauthorized packets into an established communication stream between two parties. By crafting packets that appear legitimate, an attacker can hijack sessions, deliver malware, or redirect users to malicious websites. For example, an attacker could inject a packet containing a malicious command into a remote administration session. Mitigation strategies include using firewalls with deep packet inspection, implementing Intrusion Detection Systems (IDS) to identify anomalous traffic, and enforcing strict session authentication.
DDoS Traffic Floods
In a Distributed Denial of Service (DDoS) attack, the goal is to make a service unavailable by overwhelming it with a massive volume of traffic. Attackers use botnets to send a flood of packets to the target’s IP address. Common methods include SYN floods, which exhaust server resources by sending a high volume of connection-request packets, and UDP floods, which saturate network bandwidth. Defenses require a multi-layered approach, including cloud-based DDoS mitigation services that filter malicious traffic before it reaches the network.
Source IP Spoofing
IP spoofing is the act of forging the source IP address in a packet’s header. Attackers do this to conceal their identity or to impersonate a trusted device, thereby bypassing firewall rules or authentication checks. This technique is also a critical component of DDoS amplification attacks, where requests with a spoofed source IP are sent to public servers, causing those servers to flood the victim with responses. The primary countermeasure is network-level ingress and egress filtering, which blocks packets with illegitimate source addresses from entering or leaving the network.
IP Fragmentation Attacks
These attacks exploit vulnerabilities in how a destination host reassembles fragmented IP packets. A classic example is the “Ping of Death,” where an attacker sends an IP packet larger than the maximum allowed size (65,535 bytes) by splitting it into fragments. When the target system attempts to reassemble the fragments, the oversized packet causes a buffer overflow, which can crash or destabilize the operating system. Modern systems are largely patched against this specific attack, but the principle of exploiting fragmentation remains a potential vulnerability.
ARP Cache Poisoning
This attack, also known as ARP spoofing, occurs on a Local Area Network (LAN). The attacker sends falsified Address Resolution Protocol (ARP) messages to associate their own MAC address with the IP address of a legitimate device, such as the default gateway (router). This tricks other devices on the network into sending traffic to the attacker instead of the proper destination. ARP poisoning is a common prerequisite for executing a Man-in-the-Middle attack. Network switches with Dynamic ARP Inspection (DAI) can help prevent this attack.
Man-in-the-Middle Interception
A Man-in-the-Middle (MITM) attack is when an adversary secretly positions themselves between two communicating parties, allowing them to intercept, read, modify, or inject packets without either party knowing. On a local network, this is often enabled by ARP poisoning. The attacker effectively becomes an invisible proxy, gaining complete control over the communication stream. The most effective defense against MITM attacks is the universal enforcement of end-to-end encryption (TLS/HTTPS), which ensures that even if traffic is intercepted, it cannot be read or tampered with.
Packet Structure in IPv4 Networks
An IPv4 packet is the primary data unit for the majority of today’s internet traffic. To ensure data is routed correctly and reliably, each packet is organized into a standardized structure, much like a postal package. This structure consists of three main parts: a header (the shipping label), a payload (the contents), and a trailer (an inspection seal, which is part of the encapsulating frame, not the IP packet itself).
Header Fields
The IPv4 header is a 20-byte section at the front of every packet that contains all the essential information for routing and handling. It acts as the packet’s instruction manual for network devices. The key fields are grouped by function:
- Addressing and Identification: The most critical fields are the 32-bit source IP address and destination IP address. These tell the network where the packet is coming from and where it needs to go. Additional fields identify the packet as IPv4 and specify the total packet length.
- Routing and Lifecycle: The Time-to-Live (TTL) field is a countdown timer that prevents packets from looping endlessly on the internet. Each time a packet crosses a router, the TTL value is reduced by one; if it reaches zero, the packet is discarded. The Protocol field specifies what kind of data the payload contains (e.g., TCP or UDP), telling the receiving computer how to process it.
- Fragmentation Control: Since packets may need to be split to cross certain networks, fields like Identification, Flags, and Fragment Offset provide a complete set of instructions for how to break them apart and correctly reassemble them at the destination.
- Integrity Check: The Header Checksum is a value calculated by the sender. The receiver performs the same calculation; if the values do not match, it indicates the header was corrupted during transit, and the packet is dropped.
Data Payload
The payload is the actual data being transported within the packet. This is the reason the packet exists in the first place and can be anything from a portion of an email, a chunk of a webpage, or a segment of a video stream. The size of the payload can vary, but the total packet size (header + payload) cannot exceed the Maximum Transmission Unit (MTU) of the network link, which is typically around 1500 bytes for standard Ethernet. The payload’s contents are interpreted by the destination device based on the protocol specified in the packet’s header.
Trailer
It is a critical distinction that IPv4 packets do not have a trailer. The concept of a trailer belongs to the Layer 2 frame (like an Ethernet frame) that encapsulates the IP packet for transmission over a local network. This Ethernet trailer, known as the Frame Check Sequence (FCS), contains a checksum value used for error detection across the entire frame. While the trailer travels with the packet across a specific link, it is stripped and rebuilt at each hop and is not part of the core IP packet structure itself.
In conclusion, the network packet is the fundamental unit that enables all modern digital communication. From its intricate structure to the security vulnerabilities it presents, understanding the lifecycle of a packet is essential for any technology professional. This guide from Axclusive delivers a comprehensive overview, empowering you to better manage and secure your network infrastructure.
Back to blog