What Is Overlay Network in Networking ?
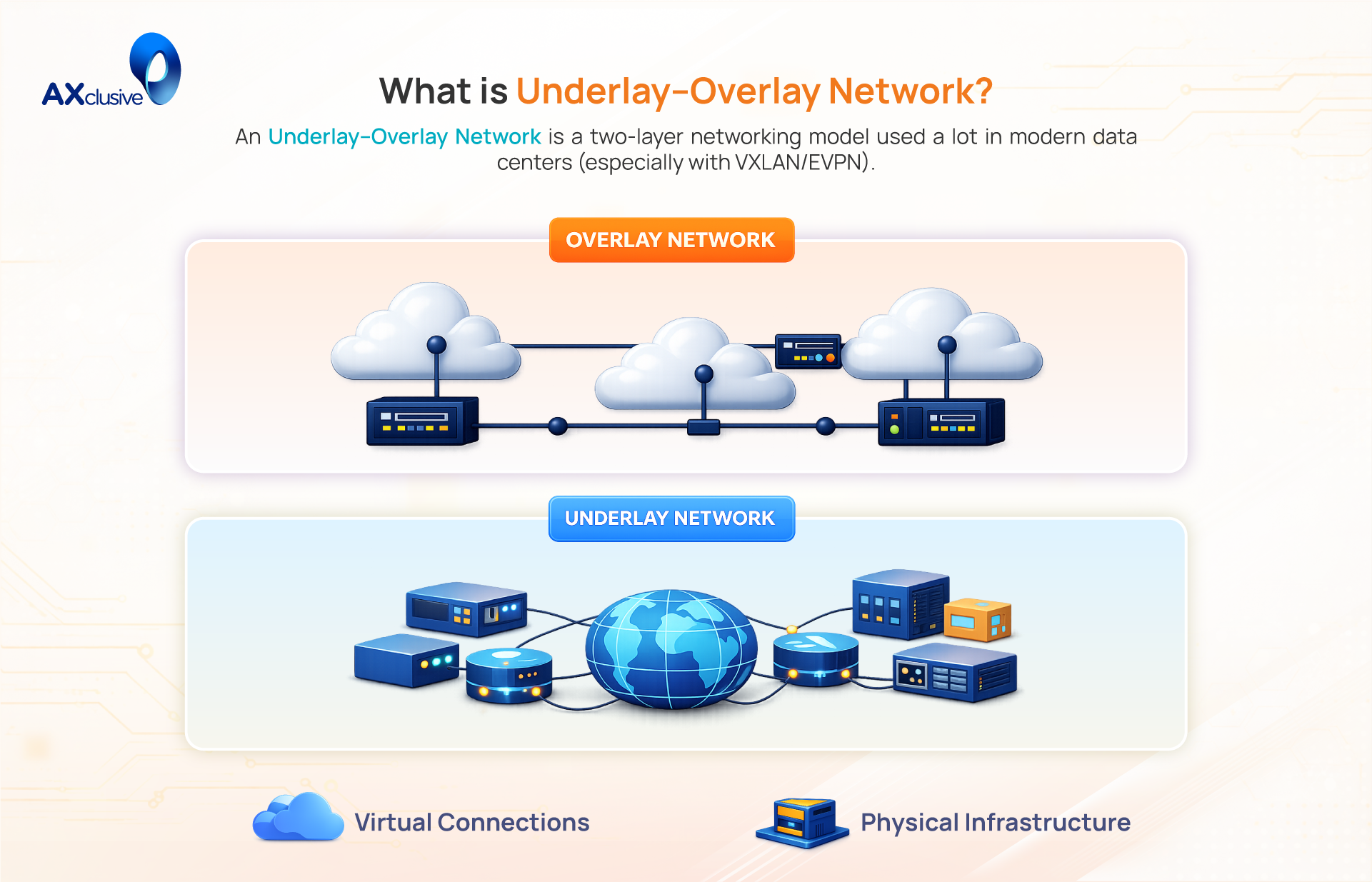
Understanding modern technologies like cloud computing and SD WAN begins with a core concept called the overlay underlay network. This layered architecture combines a virtual network with an underlying physical infrastructure to deliver flexibility and scalability. Together with Axclusive ISP explore how these network layers work in the article below.
What Is Overlay Network?
An overlay network is a virtual network created on top of an existing physical network (the underlay). It operates by encapsulating data packets from the virtual network inside packets that the physical network can understand and transport. This method decouples the logical network from the physical infrastructure. This decoupling allows administrators to create multiple, isolated virtual networks for different tenants or applications, all sharing the same physical hardware without interfering with each other.
Common Overlay Networking Technologies
Overlay networking is a broad concept implemented through various protocols, each designed to solve specific challenges. These technologies range from basic Layer 2 segmentation to complex, application-aware WAN routing, but all share the core principle of creating a logical network on top of a physical one.
Virtual LANs (VLANs)
VLANs are one of the earliest and simplest forms of network overlay. By adding an 802.1Q tag to an Ethernet frame, a single physical switch can be logically partitioned into multiple, isolated Layer 2 broadcast domains. Each VLAN acts as a distinct virtual network, preventing traffic from crossing between segments without a Layer 3 router. This provides foundational security and traffic management in nearly every enterprise network.
Generic Routing Encapsulation (GRE)
GRE is a straightforward tunneling protocol used to encapsulate one network protocol inside another. It creates a virtual point-to-point link over an IP network, allowing for the transport of otherwise non-routable traffic, such as multicast streams or legacy protocols. A GRE tunnel takes the original packet, adds a GRE header, and wraps it in a new IP header for transport across the underlay. It does not provide encryption and is often paired with IPsec for security.
Virtual Private Network (VPN)
A VPN is an overlay technology designed to create a secure, encrypted tunnel over an untrusted network like the internet. It uses protocols like IPsec to encapsulate and encrypt the original data packets, ensuring confidentiality and integrity. This is the standard technology for enabling secure remote access for employees and for connecting branch offices to a central headquarters across the public internet.
Dynamic Multipoint VPN (DMVPN)
DMVPN is a scalable solution for building large-scale VPNs. It simplifies the connection of many remote sites (spokes) to a central hub by using a combination of multipoint GRE (mGRE), IPsec for encryption, and the Next Hop Resolution Protocol (NHRP). NHRP allows spokes to dynamically discover the public IP addresses of other spokes, enabling them to build direct, on-demand tunnels. This improves performance and reduces the configuration overhead of traditional hub-and-spoke VPNs.
Virtual Extensible LAN (VXLAN)
VXLAN is the standard overlay technology for modern data centers. It overcomes the 4,094-segment limit of VLANs by using a 24-bit identifier (VNI), which allows for over 16 million isolated segments. VXLAN encapsulates Layer 2 Ethernet frames into UDP packets, allowing a single logical network to be stretched across a Layer 3 underlay. This is critical for the massive multi-tenancy and VM mobility requirements of cloud computing.
Locator/ID Separation Protocol (LISP)
LISP is a routing architecture that separates a device’s identity (Endpoint Identifier or EID) from its location (Routing Locator or RLOC). By using a distributed mapping system similar to DNS, LISP allows a device to move from one physical location to another—acquiring a new RLOC—without its identity (EID) having to change. This provides a highly flexible solution for seamless device mobility and multi-homing.
Software-Defined Wide Area Network (SD-WAN)
SD-WAN is an application-aware overlay for wide area networks. It creates a unified, centrally managed virtual network over any available underlay transport, such as MPLS, broadband, and LTE. An SD-WAN controller monitors the real-time performance of all underlay paths and intelligently routes application traffic over the best link based on predefined policies. For example, it can send critical voice traffic over a low-latency link while routing bulk data over a high-bandwidth one.
Why Overlay Networks Are Used
Overlay networks are used to overcome the inherent limitations of the physical network infrastructure. The primary driver for their adoption is the need for flexibility, scalability, and the ability to deploy new services without making costly and time-consuming changes to the underlying hardware. By creating a logical network on top of the physical one, overlays provide a layer of abstraction that allows for rapid, software-defined network changes.
Underlay Network
The underlay network is the physical foundation. It consists of the actual hardware—routers, switches, and fiber-optic cables that provides basic IP connectivity between endpoints. Its sole responsibility is to forward packets based on their destination IP address. However, this physical dependency creates several limitations:
- Rigidity: The traffic path is tied directly to the physical topology. Making changes to network services often requires re-cabling or re-configuring physical hardware.
- Lack of Segmentation: Traditional underlay networks struggle with the massive multi-tenancy requirements of modern cloud environments.
- Inefficient Multi-pathing: Load balancing traffic across multiple paths is often complex and inefficient with standard routing protocols.
Overlay Network
The overlay network is the virtual network built on top of the underlay using tunneling technologies like VXLAN or IPsec. It resolves the limitations of the underlay by creating a flexible, software-defined environment. Its key advantages include:
- Independence: The overlay’s topology is independent of the physical network. Administrators can create new logical networks, connect services, and apply policies without touching the underlay hardware.
- Scalability and Segmentation: Technologies like VXLAN allow for the creation of millions of isolated network segments, enabling massive multi-tenancy on a shared physical infrastructure.
- Enhanced Security: Overlays like VPNs can encrypt traffic, ensuring secure communication even when traversing an untrusted underlay like the public internet.
- Intelligent Traffic Management: Modern overlays, particularly SD-WAN, can intelligently route traffic across multiple underlay paths, optimizing performance and maximizing bandwidth utilization based on real-time conditions.
What is an underlay network?
An underlay network is the physical infrastructure that provides the foundation for all network communication. It consists of tangible hardware like routers, switches, and optical fiber, which are interconnected to form a basic IP transport fabric. The primary and sole responsibility of the underlay is to ensure that any two points on the network can exchange IP packets. It is built upon standard routing protocols and physical transport technologies like Ethernet and MPLS. The performance, capacity, and reliability of this physical underlay directly determine the potential of any virtual overlay network built upon it.
Underlay vs overlay network
The fundamental difference between an underlay and an overlay network is the separation of the physical infrastructure from the virtual services running on top of it. The underlay provides the basic transport, while the overlay delivers the intelligent features.
| Feature | Underlay Network | Overlay Network |
|---|---|---|
| Core Role | The physical infrastructure responsible for delivering packets from one point to another. | The virtual architecture built on top of the underlay to provide advanced services. |
| Components | Physical hardware such as routers, switches, and optical fiber. | Logical constructs like virtual switches, tunnels, and software-defined policies. |
| Primary Function | Provides foundational IP reachability and packet forwarding. | Delivers services like multi-tenancy, segmentation, encryption, and traffic steering. |
| Agility | Inflexible. Changes to topology or services require physical hardware reconfiguration. | Highly agile. Network services and topology can be modified instantly through software. |
| Awareness | Unaware of the overlay. It only sees standard IP packets and forwards them normally. | Aware of the underlay’s performance and uses it as a transport medium. |
| Protocols | Standard routing protocols (e.g., OSPF, BGP) and transport technologies (e.g., Ethernet). | Tunneling and encapsulation protocols (e.g., VXLAN, IPsec, GRE). |
| Management | Managed on a device-by-device basis through traditional network management systems. | Centrally managed and automated through a software-defined controller (e.g., SDN, SD-WAN). |
The separation of the physical underlay from the virtual overlay is the foundational principle behind modern network agility and scale. While the underlay provides the essential IP transport, the overlay delivers the intelligent, on-demand services required by cloud, SD-WAN, and secure access solutions. This guide from Axclusive provides the clear understanding needed to design and manage these sophisticated, two-layer architectures effectively.
🌐 Contact us today to learn more about what is an overlay network and how overlay and underlay architectures can improve network flexibility and performance.
Back to blog