What Is DDoS Protection and Why It Matters?
In an era where digital presence determines business success, a single malicious traffic surge can cause devastating downtime. To defend your infrastructure, you must first understand what is DDoS protection. This multi-layered defense strategy acts as a critical shield, filtering out harmful request floods while ensuring your services remain available to legitimate users. Join Axclusive ISP in the article below as we explore the essential best practices and industry-leading platforms to fortify your network against modern cyber threats.
What is DDoS Protection?
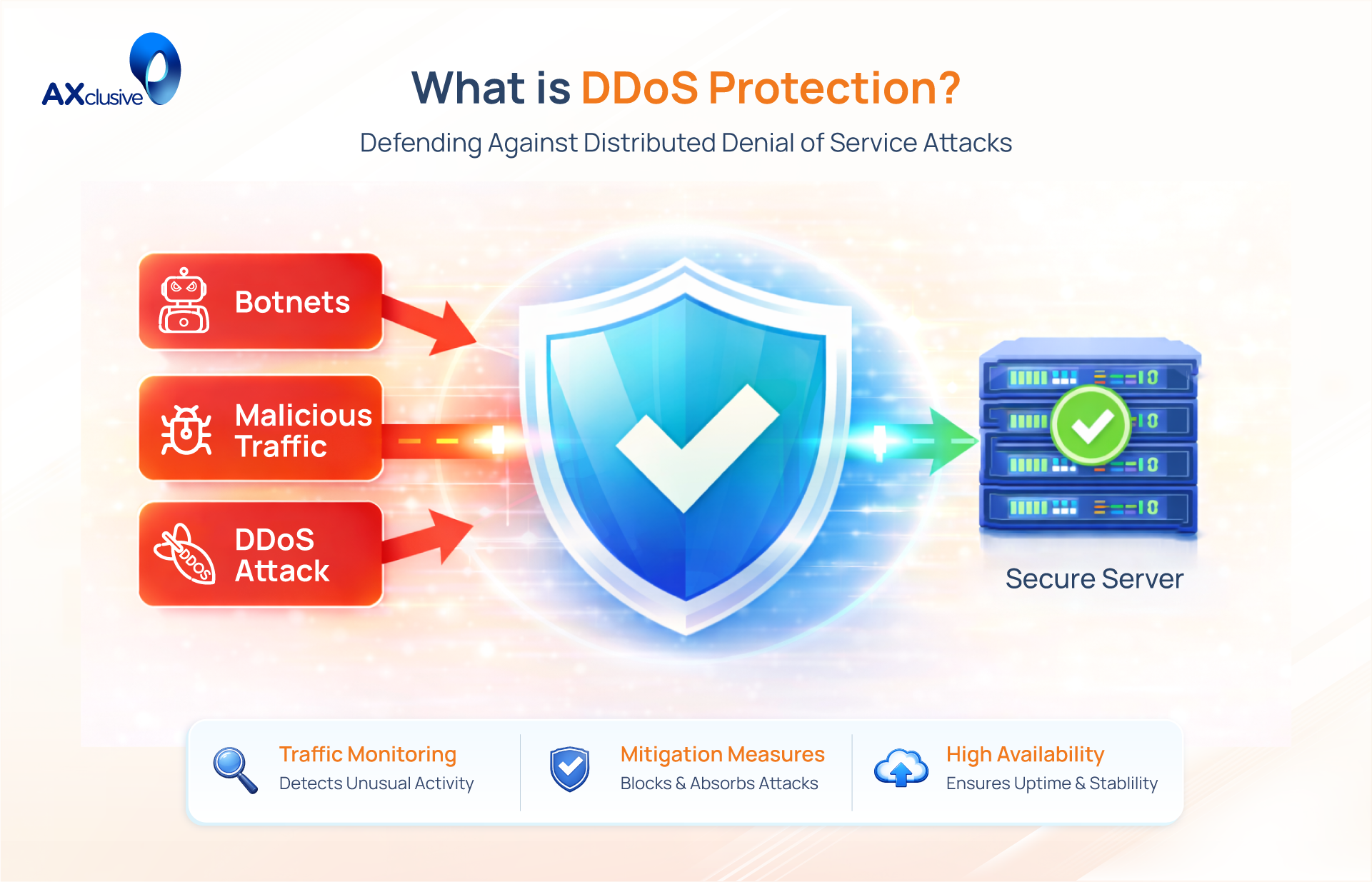
DDoS protection is a comprehensive set of techniques and tools designed to defend a network, server, or application from a Distributed Denial-of-Service attack. A DDoS attack occurs when a malicious actor overwhelms a target with a flood of illegitimate internet traffic. This flood consumes all available bandwidth or server resources, making the service unavailable to legitimate users. Effective protection is critical because a successful attack can severely damage a company’s reputation and lead to significant financial losses.
The core challenge of what is ddos protection lies in distinguishing bad traffic from good traffic. A sudden surge in visitors could be a viral marketing success or the beginning of an attack. DDoS protection systems use advanced analysis to identify the malicious patterns within the traffic flood. Once identified, the system filters out the bad requests while allowing legitimate users to continue accessing the service without interruption.
How DDoS Protection Works Against Modern Attacks
DDoS protection operates as a sophisticated filtering system designed to distinguish legitimate human users from malicious automated traffic. The entire process functions on a principle of real-time analysis and mitigation, ensuring the targeted service remains available during an attack. It follows a structured, three-stage defense protocol.
- Detection: The system constantly monitors inbound traffic patterns to establish a baseline of “normal” behavior. When a sudden, anomalous spike in requests occurs, advanced algorithms analyze the traffic signature to determine if it is a legitimate surge or a coordinated attack. This detection process must be fast and accurate to initiate a defense before server resources are exhausted.
- Filtering: Once an attack is confirmed, the system diverts all incoming traffic to a specialized “scrubbing center.” In this high-capacity environment, a series of filters are applied to the data stream. These filters are designed to drop packets that match known attack patterns—such as volumetric floods (UDP floods), protocol attacks (SYN floods), or application-layer attacks (HTTP GET floods)—while identifying and allowing legitimate requests to pass through.
- Forwarding: Only the “clean” traffic that has passed through the scrubbing process is forwarded to the intended destination server. This ensures that the server’s resources are dedicated solely to serving real users, not to processing a flood of malicious requests. The end-user is often completely unaware that an attack is happening, experiencing only normal service availability.
DDoS Protection Best Practices for Stronger Network Defense
Effective DDoS protection is not a single product but a continuous strategy. A resilient defense requires a multi-layered approach that combines proactive monitoring, intelligent resource allocation, and robust security hygiene. By implementing these best practices, organizations can significantly reduce their vulnerability to attacks and ensure business continuity.
Establish Baseline Traffic Behavior
You cannot defend against what you cannot see. The first step in any effective DDoS strategy is to establish a clear baseline of your network’s normal traffic patterns. By continuously monitoring inbound and outbound data flows, you can create a detailed profile of what “normal” looks like. This includes understanding peak usage times, common geographic sources of traffic, and typical packet sizes. This baseline allows your detection systems to instantly recognize anomalous spikes that deviate from the norm, enabling a faster and more accurate response when an attack begins.
Prioritize Mission-Critical Assets
Not all systems are created equal. In the event of an attack, you must know which assets are most critical to your business operations. Maintain an up-to-date inventory of your essential infrastructure, including web servers, application APIs, and DNS servers. This prioritization allows you to apply the strongest and most immediate protection to the services that directly impact revenue and customer experience. During an attack, resources are finite; knowing where to focus them is essential for effective mitigation.
Strengthen Network Security Controls
Basic network security is a critical foundation for DDoS defense. A well-maintained network is inherently more resilient. This involves a commitment to consistent security practices across the organization:
- Regular Patch Management: Keep all servers, routers, and firewalls updated with the latest security patches to close known vulnerabilities.
- Access Control: Implement strong password policies and multi-factor authentication (MFA) to prevent unauthorized access to network devices.
- Firewall and Antivirus: Deploy and maintain properly configured firewalls and up-to-date antivirus software on all endpoints.
- Employee Training: Educate employees on security best practices to prevent them from inadvertently compromising the network.
Expand Capacity for Traffic Surges
While it is not a complete solution on its own, having excess bandwidth can provide a crucial buffer during the initial moments of a volumetric DDoS attack. Provisioning more network capacity than you need for daily operations can help absorb smaller attacks without immediate service degradation. This “overprovisioning” gives your detection and mitigation systems valuable time to identify and filter the malicious traffic before your resources are completely exhausted. However, it is important to note that bandwidth alone cannot stop a large-scale attack; it must be paired with an intelligent filtering solution.
DDoS Protection Platforms Overview
Selecting a DDoS protection platform requires evaluating your infrastructure’s specific needs, whether you operate entirely in the cloud, rely on on-premises hardware, or maintain a hybrid environment. The following market-leading solutions offer diverse architectures, from anycast-based global edge networks to dedicated scrubbing centers.
Cloudflare Magic Transit
Cloudflare operates the industry’s largest anycast network, spanning over 330 cities. Magic Transit protects entire IP prefixes by inspecting traffic inline at the network edge, eliminating the need for traffic diversion to a separate scrubbing center.
- Best For: Enterprises requiring massive mitigation capacity and flat-rate, predictable pricing.
- Key Advantage: Sub-3-second detection and 405+ Tbps total capacity.
- Architecture: Anycast-based routing combined with inline, edge-level inspection.
Akamai Prolexic
Akamai Prolexic is the established standard for organizations demanding the highest level of human-managed security. It utilizes a global network of dedicated scrubbing centers to divert and clean traffic before returning it to the origin.
- Best For: Tier-1 financial institutions, government agencies, and critical infrastructure.
- Key Advantage: A 100% uptime SLA and 24/7 staffing by a dedicated Security Operations Command Center (SOCC).
- Architecture: BGP-based traffic diversion to centralized high-capacity scrubbing centers.
AWS Shield Advanced
AWS Shield Advanced is purpose-built for organizations hosting their entire stack within the Amazon Web Services ecosystem. It provides native, always-on detection and mitigation for L3/L4 and L7 attack vectors.
- Best For: Organizations exclusively hosted on AWS.
- Key Advantage: Unique “cost protection,” which reimburses customers for AWS scaling charges triggered by DDoS traffic.
- Architecture: Native integration with CloudFront, Route 53, and EC2 utilizing telemetry across the entire AWS ecosystem.
Radware Cloud DDoS Protection
Radware provides a sophisticated hybrid model that combines on-premises hardware (DefensePro) with cloud-based scrubbing centers. This approach is highly effective for organizations with strict data residency requirements or complex 5G network infrastructures.
- Best For: Telecommunications carriers and ISPs requiring local and cloud-based defense.
- Key Advantage: Patented behavioral analysis that reduces false positives without manual rule tuning.
- Architecture: A hybrid deployment combining inline hardware detection and global cloud scrubbing.
Imperva DDoS Protection
Imperva offers a unified platform that consolidates DDoS mitigation, Web Application Firewall (WAF), and Bot Management. It is a preferred “single-vendor” solution for complex web-facing environments.
- Best For: E-commerce, healthcare, and financial services needing full-stack web security.
- Key Advantage: Machine learning-based policies that automatically tune themselves, significantly reducing operational management effort.
- Architecture: Globally distributed scrubbing centers combined with integrated CDN and application-layer security.
DDoS Protection Side by Side Comparison
| Criteria | Cloudflare Magic Transit | Akamai Prolexic | AWS Shield Adv. | Radware Cloud | Imperva |
|---|---|---|---|---|---|
| Network Capacity | 405+ Tbps ✓✓✓ | 20+ Tbps ✓✓ | Not published | 15 Tbps ✓ | Not published |
| Global PoPs / Centers | 330+ cities ✓✓✓ | 32 scrubbing ✓✓ | All AWS regions | 21 centers ✓ | 44+ centers ✓✓ |
| Mitigation Speed | < 3 sec avg | 0-sec (proactive) | Seconds (auto) | Real-time SLA | < 3 sec SLA |
| Architecture | Anycast inline | BGP scrubbing | AWS-native | Hybrid on-prem + cloud | Cloud scrubbing |
| L3/L4 Protection | Yes | Yes | Yes | Yes | Yes |
| L7 Protection | Via Magic Firewall | Via App & API Protector | Via AWS WAF | Via WAF add-on | Yes (integrated) |
| Managed SOC | Limited (Enterprise) | 24/7 dedicated SOC | DRT (24/7 Adv) | 24/7 ERT | Via managed plans |
| On-Premises Support | No (cloud only) | Yes (Prolexic On-Prem) | No (AWS only) | Yes (DefensePro) | Limited |
| Hybrid Support | Yes (GRE/IPsec) | Yes | AWS-centric | Yes (best-in-class) | Yes |
| BGP Integration | Native full support | Yes (scrubbing) | Limited | Yes | Yes |
| Pricing Model | Flat monthly (custom) | Custom enterprise | $3,000/mo fixed | Custom / marketplace | Custom enterprise |
| Overage Fees | None | May apply | Cost protection | Custom | Custom |
| Self-Service / API | Strong (BYOIP API) | Limited | AWS Console/API | Moderate | Moderate |
| BYOIP Support | Yes (/24 minimum) | Yes | Yes (AWS IPs) | Yes | Yes |
| Market Mindshare | 18.8% (DDoS) | 4.2% | Large (AWS-bound) | Mid-market | Mid-market |
| Best For | All-purpose enterprise | Finance / gov / critical | AWS workloads | Carrier / telco / hybrid | Multi-layer / SME |
Proactive DDoS protection is essential for a resilient digital infrastructure. By establishing traffic baselines, prioritizing critical assets, and deploying the right mitigation platform, you can successfully defend against sophisticated cyber-attacks. Axclusive trusts this guide provides the foundational knowledge needed to fortify your network and ensure continuous uptime for your business.
🛡️ Discover what is DDoS protection and keep your network secure. Contact us to strengthen your defense against modern attacks. 🚀
Back to blog