What Is Cloudflare Magic Transit?
DDoS attacks now pose an existential risk to enterprise connectivity. To defend your infrastructure without sacrificing performance, you need to understand what is Cloudflare Magic Transit. It serves as a global, cloud-native shield that filters malicious traffic at the edge while accelerating legitimate data flows. Join Axclusive ISP in this article to explore how this platform secures your IP network and optimizes performance in a rapidly escalating threat landscape.
What is Cloudflare Magic Transit?
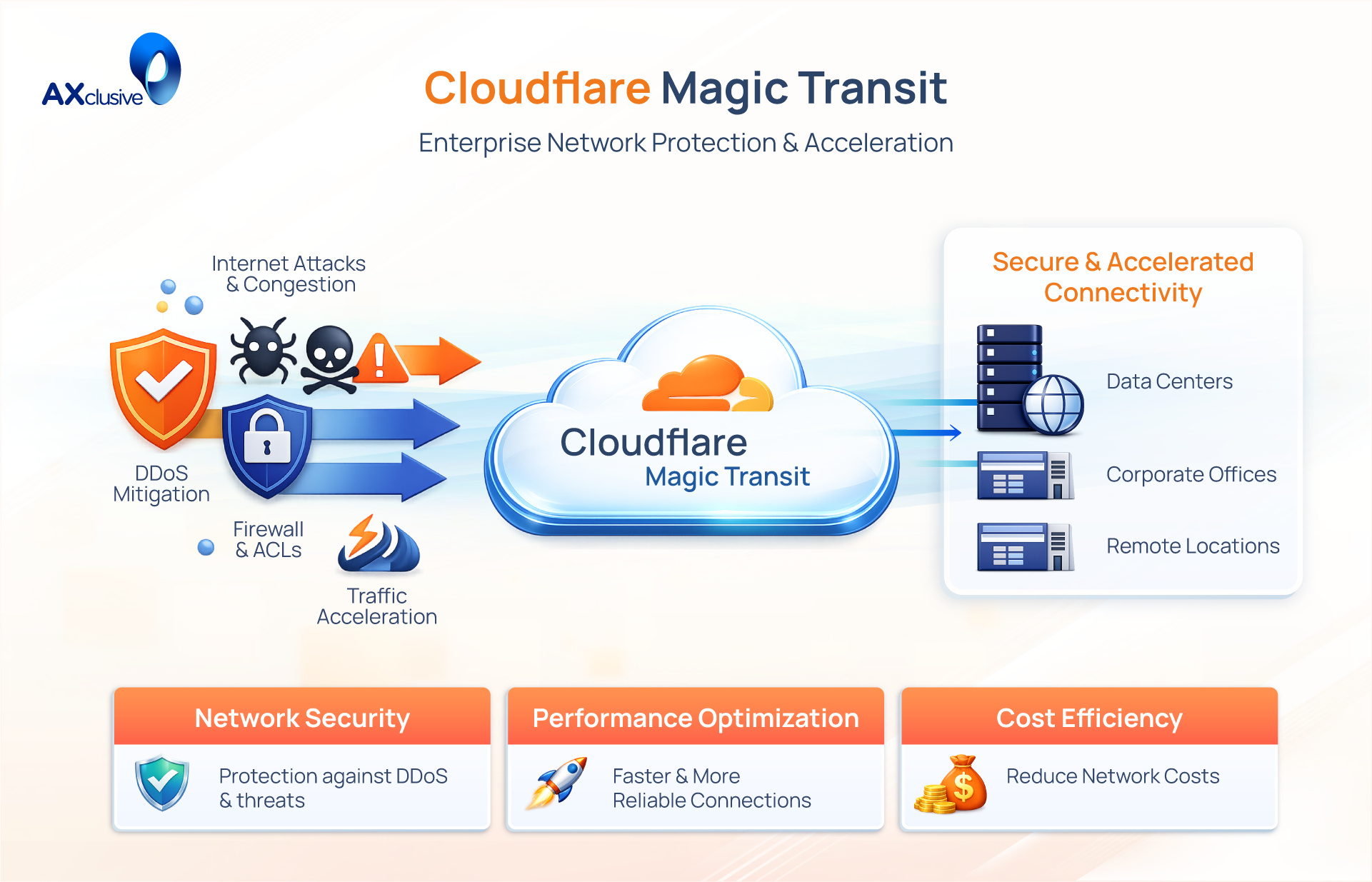
Cloudflare Magic Transit is a cloud-native security and performance platform designed to protect entire IP networks from large-scale volumetric DDoS attacks. Unlike traditional solutions that rely on localized hardware or distant scrubbing centers, Magic Transit leverages Cloudflare’s global anycast network to inspect and filter inbound traffic directly at the edge. By sitting in front of your on-premises, cloud-hosted, or hybrid infrastructure, it absorbs malicious floods globally across 330+ cities while simultaneously accelerating legitimate data flow. This architecture eliminates the latency penalties common in legacy security models, providing an always-on, high-capacity shield that scales to meet the rapidly escalating volume of modern network-layer threats.
How Magic Transit Works
Magic Transit works by taking over the announcement of your IP address space on the global internet using Border Gateway Protocol (BGP). Instead of your traffic traveling directly to your data center, it is first ingested by the nearest Cloudflare point of presence, processed, and then delivered to you through an encrypted tunnel. The process can be broken into three core phases:
Connect — BGP Route Announcement
Cloudflare announces your company’s IP prefixes to the internet via BGP from every one of its global data centers simultaneously. This is done using anycast routing, meaning that traffic destined for your IPs is automatically attracted to the Cloudflare data center geographically closest to the traffic source. Your organization stops advertising those prefixes directly to your own ISPs, making Cloudflare the authoritative entry point for all inbound traffic.
Protect and Process — Real-Time Inspection
Once packets arrive at a Cloudflare data center, every packet is inspected in real time. Cloudflare’s automated DDoS mitigation engine applies multi-layer analysis including rate limiting, anomaly detection, traffic pattern analysis, and AI-driven threat intelligence to distinguish legitimate traffic from attack traffic. Malicious packets are dropped at the edge, close to their source, typically within three seconds of attack detection globally on average.
In addition to DDoS mitigation, administrators can apply advanced network firewall rules, access control lists, geo-blocking, and traffic steering policies through the Cloudflare dashboard or API, giving teams fine-grained control over what reaches their infrastructure.
Accelerate — Clean Traffic Delivery
Once traffic is verified as clean, Cloudflare forwards it to your origin network over secure tunnels — either GRE (Generic Routing Encapsulation) or IPsec — or via private network interconnects (PNI) through Cloudflare Network Interconnect (CNI). Cloudflare’s backbone routes this clean traffic over optimized, low-latency paths, often delivering better performance than the public internet alone.
Key Features and Capabilities
Cloudflare Magic Transit transforms network defense by shifting security from localized appliances to a globally distributed edge. By leveraging its anycast network, the platform provides scalable, wire-speed mitigation without the latency penalties inherent in traditional scrubbing centers.
Massive DDoS Mitigation Capacity
With a total capacity exceeding 405 Tbps, Magic Transit is built to absorb the largest volumetric DDoS attacks in history. Because the network is globally distributed, malicious traffic is mitigated at the edge closest to its source preventing it from ever reaching your origin servers. This scale ensures that even multi-terabit floods are neutralized instantly without requiring hardware upgrades.
Sub-3-Second Global Mitigation
Speed is the defining factor in successful DDoS defense. Magic Transit detects and mitigates threats in under three seconds on average. By performing “inline” inspection directly at the edge, it eliminates the minutes-long redirection delays required by legacy scrubbing centers, keeping your applications online even during the initial surge of an attack.
Network-Level Firewall as a Service
Magic Firewall is integrated directly into the Magic Transit platform. It allows administrators to enforce packet-level rules based on IP, protocol, port, and packet length at every one of Cloudflare’s global locations. This provides a cloud-native “Firewall as a Service” (FWaaS) that updates instantly via dashboard or API, securing your network without the need for manual on-premises ACL updates.
Direct Server Return (DSR) Architecture
Magic Transit defaults to Direct Server Return (DSR) mode, where only inbound traffic passes through Cloudflare for inspection. Return traffic from your servers travels directly to the user via your local ISP. This architecture significantly reduces latency and removes the performance bottlenecks associated with “hairpinning” outbound data through a security provider.
Anycast GRE and IPsec Tunnel Support
Connectivity is simplified through anycast GRE or IPsec tunnels. You configure a single tunnel on your network, and that tunnel automatically connects to all Cloudflare data centers globally. This design provides built-in redundancy; if one data center is unreachable, traffic instantly reroutes to the next closest location without you having to reconfigure local tunnel settings.
BGP Peering and Dynamic Routing
For enterprise-grade control, Magic Transit supports BGP peering between your infrastructure and Cloudflare. This enables dynamic route advertisement, which ensures that traffic always follows the most optimal path. BGP peering also allows for automated failover and session recovery, treating your network and Cloudflare’s as a seamless, integrated peer.
Cloudflare Network Interconnect
Organizations requiring the highest level of performance can utilize Cloudflare Network Interconnect (CNI). This feature provides dedicated physical or virtual private connections between your infrastructure and Cloudflare, bypassing the public internet entirely. Express CNI can be provisioned in minutes via the dashboard, ensuring a stable, low-latency transit path for your encapsulated traffic.
Magic Network Monitoring
Magic Network Monitoring provides end-to-end traffic visibility by analyzing NetFlow, sFlow, and IPFIX data. It acts as a centralized telemetry tool that allows engineers to visualize attack patterns and investigate anomalies in real time. Because it processes flow data from your edge, you gain deep insights into your network health without deploying extra on-premises sensors.
Magic Transit vs Traditional DDoS Protection
How Magic Transit compares to legacy scrubbing center and on-premises hardware approaches:
| Capability | Magic Transit | Traditional Scrubbing Center | On-Premises Appliance |
|---|---|---|---|
| Mitigation Capacity | 405+ Tbps | Limited by provider capacity | Limited by hardware specs |
| Detection Speed | < 3 seconds globally | Minutes (traffic diversion) | Seconds (but local only) |
| Latency Impact | Minimal / often improves | High (rerouting adds RTT) | Low (inline) |
| Hardware Required | None | None | Expensive, ongoing CAPEX |
| Scalability | Automatic with CF network | Manual capacity upgrades | Hardware refresh cycle |
| Global Coverage | 330+ cities worldwide | Limited PoPs | Data center only |
| Management | API / Dashboard | Vendor portal | CLI / vendor tooling |
| BGP Integration | Native support | Varies by vendor | Varies |
| Pricing Model | Flat monthly rate | Bandwidth overage fees | CapEx + maintenance |
Cloudflare Magic Transit Deployment Architecture Models
Magic Transit offers flexible deployment architectures to fit diverse network requirements. Whether you need to minimize latency for outbound traffic or demand full bidirectional inspection, the platform adapts to your existing infrastructure.
Ingress Only
This is the default and most popular deployment model. Incoming internet traffic is routed through Cloudflare for DDoS inspection and mitigation before reaching your network via GRE or IPsec tunnels. Crucially, your server return traffic bypasses Cloudflare, going directly to the user via your local ISP. This approach significantly reduces latency by eliminating unnecessary traffic hairpinning.
Full Proxy
In full proxy mode, both inbound and outbound traffic are forced through Cloudflare’s global edge. This is achieved by configuring policy based routing on your edge devices to tunnel all outgoing packets. This model is ideal for organizations requiring comprehensive visibility and deep inspection of all network flows, providing granular control over every packet entering or leaving the environment.
Bring Your Own IP
Organizations that own their public IP address space can onboard their own prefixes directly into the Magic Transit platform. Cloudflare provides a self service API that allows you to manage and announce your IP ranges programmatically. This gives you full control over your address space without relying on provider assigned IPs, ensuring consistent network identity across all deployments.
Cloudflare Managed IP Space
For smaller networks that lack the required minimum IP prefix size, Cloudflare provides managed IP space. This allows smaller organizations to leverage the full suite of Magic Transit security features, including firewall as a service and DDoS mitigation, without needing to own or manage their own registered IP address blocks. It provides enterprise grade protection to networks of any size.
Cloudflare Magic Transit Performance Considerations
A common concern with network-level security is the potential for increased latency. Magic Transit addresses this by moving inspection inline, ensuring security measures do not create bottlenecks. In fact, many organizations report improved performance after deployment because their traffic traverses Cloudflare’s optimized global backbone rather than the unpredictable public internet.
The architecture focuses on three performance-critical pillars:
- Optimized Routing: Cloudflare utilizes Anycast routing, which forces inbound traffic to enter the network at the data center geographically closest to the user. This eliminates unnecessary long-distance detours and minimizes the physical round-trip time.
- High-Speed Backbone: Data centers are linked via dedicated, low-latency private fiber. These internal paths often outperform the congested public internet, providing a faster “fast lane” for your traffic to reach its destination.
- Inline Mitigation: Security inspection happens in real-time as packets traverse the edge. Because Magic Transit does not divert traffic to a distant, centralized scrubbing center, there is no “hairpinning” delay. Your data is cleaned instantly and forwarded without the typical latency overhead of legacy DDoS platforms.
- Direct Server Return (DSR): By default, outbound traffic from your servers bypasses Cloudflare and travels directly to the user. This ensures your outbound performance remains entirely under your control, preserving the original throughput of your ISP link.
Cloudflare Magic Transit represents a definitive solution for modernizing enterprise network defense. By shifting security to a massive, anycast-enabled global edge, it eliminates the latency of legacy scrubbing centers while guaranteeing enterprise-grade DDoS mitigation. Axclusive trusts this guide has provided the foundational knowledge required to fortify your IP infrastructure and ensure your services remain secure, fast, and fully available.
